The Ubiquiti Diaries: A Site-to-Site VPN Story
by Ganesh T S on December 21, 2022 8:00 AM EST- Posted in
- Networking
- Ubiquiti Networks
- UniFi
- VPN
Miscellaneous Considerations and Concluding Remarks
The site-to-site VPN setup created with the help of ZeroTier is able to provide easy access to systems in both sites without involving a relay in the middle. Remote management of systems connected to the UDM from the US is straightforward - essentially dealing with something in the local LAN. The need for port forwarding and other overheads is done away with. Performing offsite backups is also simplified. A NAS connected to the UDM is equivalent to a NAS connected to the USG Pro 4 as far as backup jobs go, as all the routing is handled transparently within the USG Pro 4 and the UDM. The two remaining aspects I set out to achieve - seamless utilization of OTT services on either side (particularly, Indian ones on the US side) and transparent extension of the Indian Wi-Fi network in the US were achieved only on a per-device basis (by configuring a proxy). My next step was to address that by creating a wireless network on the USG Pro 4 that would defer to the UDM as the gateway.
Policy-Based Routing on the USG Pro 4
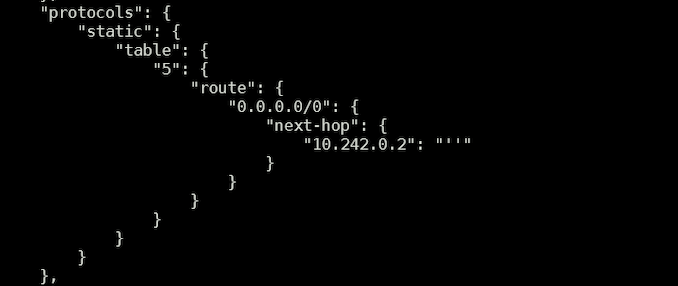
The first step involved the configuration of a new network in the web UI, followed by creating a new Wi-Fi SSID and allocating the new network to it. In my case, the new network was allocated VLAN ID 5. The USG was allowed to provision itself after these changes before moving on to the next step. Using the same config.gateway.json scheme adopted for task scheduling, a new routing table was created with the default route pointing to the ZeroTier IP of the UDM deployed in India.
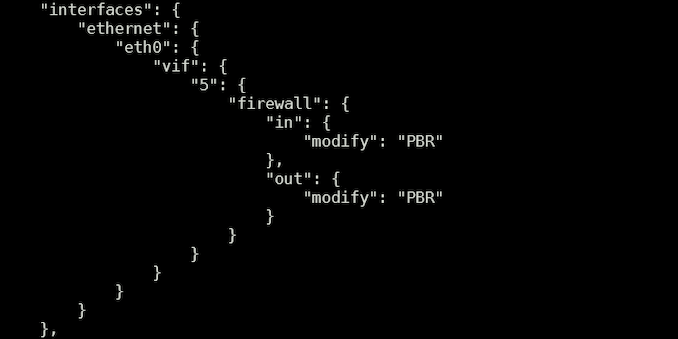
The next step involved creation of new firewall rules with the modify tag. All VLANs except for the newly created one with ID 5 were relegated to the usage of the main routing table. The new VLAN alone (singled out using the source address subnet) was allocated the newly created routing table. Most importantly, source validation was disabled.
Finally, the new firewall rules were allocated to the newly created VLAN.
Upon provisioning the new configuration, the new Wi-Fi SSID became equivalent to the one on the UDM side. For all practical purposes, clients connecting to that SSID appeared to be accessing the web from an Indian IP address. This method of VPN access also circumvents checks put in by some OTT apps, wherein streaming would get disabled upon the recognition of any VPN profile on the device.
Future Work
The satisfaction of getting the site-to-site VPN working aside, I am not particularly happy that I had to involve a third-party service in the mix. Eventually, I would like to get either manual IPSec or WireGuard working. Both are suppoed to not have trouble with the public WAN IP side acting as a server and the machine behind the CGNAT acting as a peer as long as the required ports are open. However, I have not had much luck (as described in detail in the IPSec section). WireGuard debugging is also complicated by the fact that the USG Pro 4 is a relatively closed system (enabling kernel level debugging of WireGuard using the recommended scheme doesn't work).
Given that I am not a professional network administrator, it is entirely possible that there is a much simpler solution for my requirements here - experienced readers are welcome to provide suggestions in the comments.
Final Words
Ubiquiti's UniFi lineup is immensely popular among prosumers, and enjoys a cult following. It is easy to see why - simple aspects are easy to configure over the web UI, while SSH access is available for the more esoteric things. At the same time, the relationship is a bit frustrating too (the propensity of the gateways to corrupt themselves at the drop of a hat in the event of a power failure, and the UDM being silent about unsuccessful NTP synchronization attempts are cases in point). On balance, I would still recommend Ubiquiti equipment, and upgrades to my primary deployment of the USG Pro 4 and host of Wi-Fi 5 APs are likely to be UniFi-based in the future.
Back in 2017 (when I decided to go with UniFi for my residential installation), the concept of economical managed SDN solutions for prosumers was in its infancy, with Ubiquiti's offerings being the only game in town. Since then, we have seen other vendors step in with their own suite of products - Netgear's Insight-managed business networking products, TP-Link's huge Omada line-up with support for both cloud-based and local management controllers, and QNAP's set of products supporting QuWAN are examples. In light of the increased competition, Ubiquiti would do well to address some of the pain points outlined in this article. In particular, the absence of a guaranteed upgrade path for customized USG Pro 4 installs like the one above to one of the newer AArch64-based gateways is a cause of concern. There are also features taken for granted (like the NTP server functionality in the USG Pro 4) that are not present in the newer gateways. Considering that Ubiquiti has opted for a container-based architecture in the UDM and subsequently released UniFi gateways, they might as well create an official curated app store to enable additional functionality.
Moving forward, I hope to address other interesting aspects of Ubiquiti's lineup of products in this series of articles. Suggestions from readers are welcome.












35 Comments
View All Comments
prophet001 - Wednesday, December 21, 2022 - link
Not really a ubiquiti fan.Threska - Wednesday, December 21, 2022 - link
Ubiquiti vacuum.OddballSix - Wednesday, December 21, 2022 - link
There's no point in even talking about Ubiquiti, you can't buy most of their products. Some of them have been out of stock in the entire channel for months.Entire parts and lines of products gone. You can't buy them. One breaks? You're screwed. Need to upgrade the firewall? Tough.
HalcyonDays - Wednesday, December 21, 2022 - link
I actually went down a similar path as you did. Years ago, when I moved out, I needed away to troubleshoot my parents network remotely when I inevitably get the dreaded phone call "internet is not working".My requirements for this setup are as follows:
1. Bidirectional encrypted tunnel(s) - preferably peer-to-peer
2. No third-party cloud services
3. Each site access internet through their its own ISP
4. Router at each site will handle the VPN connection - no additional hardware
After attempting and investigating multiple methods, I eventually settled on "tinc" based on the suggestion from the openwrt forums.
"tinc" is a peer-to-peer VPN supported by Tomato, Openwrt, and asuswrt-merlin. It doesn't need all sites to have public IP to work. It just need one site to have public IP (I think). To handle dynamic IPs, I use a free DDNS service and assign a domain name to each of the site.
Since then, I have expanded VPN network to include the in-laws and parents' home in Taiwan. It just required the router at each site to have the public key of at least one other site and it'll be able to see all sites. This means that I can be at any of these sites and still see every site.
Some caveats: I am uncertain of the performance. From what I can tell, "tinc" is pretty lightweight but not as performant as wireguard. Because I don't stream anything over tinc tunnels, I can't vouch for how well it works for for that.
Give it a try.
Samus - Thursday, December 22, 2022 - link
Amazing hardware and stability totally ruined by crap software. The controller is trash. Relying on Java is already a red flag but the way the controller database functions is bazaar and totally insecure. Inheriting\adopting hardware into a new instance results in a mandatory config wipe. No fortune 500 or enterprise network would use this so what really separates it from a $100 consumer product? A consumer product that often has more basic functionality; Ubiquiti has to this day failed to implement MAC cloning, axing it from consideration to anybody who has AT&T or Verizon fiber that need to emulate their gateway from the ONT\media converter. Such a basic feature dating back to the Linksys routers of the 90's missing from a $300 prosumer product is embarrassing and should alone put the company underwater. I mean why?Hamm Burger - Thursday, December 22, 2022 - link
My ISP provides CGNAT by default, but one can pay extra (€1.95/month afair) for a non-fixed but routable address. Which I do. Of course, you have to to know that you can ask, because they don't advertise this feature.Samus - Saturday, December 24, 2022 - link
That is cheap. Commercial block IP's are rarely offered in the US to residential subscribers, and even 'business' internet plans find a way to screw you out of $15 minimum for a "usable" static address.It's worth noting over the years I've seen most IP addresses - even for residential internet - have become statically assigned to subscribers, but they are non-routable.
ballsystemlord - Thursday, December 22, 2022 - link
@Ganesh , why not just contact the ISP and tell them that you were paying for an IP address that is *not* behind CGNAT? I mean, if you're spending the money for the IP you should get it.Jorgp2 - Thursday, December 22, 2022 - link
Yup, or just pay for a /29 or something.coburn_c - Thursday, December 22, 2022 - link
ipv6 is dead and rightly so